Pickup, Repair & Delivery: The IT support team is available today from 8:30 a.m. to 11 p.m.
Specialized IT service in the legal, real estate, construction, automation, retail, and entrepreneurial fields in Quebec.
Three easy steps to get ON-SITE support:
1- Call us now (We accept SMS) and tell us details about your request
2- Make an appointment at your convenience
3- We will arrive at the scheduled time
Three easy steps to get REMOTE support:
1- Call us now
2- Run the express support software
3- Let our best technician guide you 😉
The fastest service.
For remote support. See conditions

Proven Expertise in IT Support for Notaries in Quebec - ProCardex Cloud, ConsignO, TELUS Assyst Immobilier, Office 365, and more.
"Join the growing network of Quebec notaries who trust our specialized IT support. Our expertise with ProCardex Cloud, ConsignO, TELUS Assyst Immobilier, and Office 365 ensures improved technological management. Entrust your IT tools to us for a more efficient and secure notarial practice."
General services:
|
Services |
Description |
|
Quick Assessment |
Enjoy a top-tier troubleshooting service tailored to your budget and time constraints. |
|
Device Configuration |
Our specialists are eager to set up your electronic devices, regardless of the operating system. |
|
Malware Removal |
Efficient virus and spyware removal and prevention without data loss, using the best software available. |
|
Printer Setup |
Offering installation, maintenance, or repair services for your printer, either onsite at your home or remotely online. |
|
Network Troubleshooting |
Our qualified technicians are ready to diagnose and fix your wired or wireless network issues. |
|
System Update |
Enhance features and improve the efficiency or performance of your computer. |
|
Computer Cleaning |
Is your machine slow or running out of space? Maybe it's time for a cleanup. |
|
Data Backup |
Rest easy with our data protection and backup services for your essential data. |
|
Software Installation |
Need help installing software? Whether it's an operating system or something else, we've got you covered. |
Enterprise Services:
|
Services |
Description |
|
Enterprise IT Support |
Comprehensive IT support services tailored to meet the unique needs of your business, ensuring minimal downtime. |
|
Managed IT Services |
Proactive management of your IT infrastructure and systems to improve operational efficiency and reduce risks. |
|
Cloud Solutions |
Customized cloud services to enhance collaboration, data accessibility, and scalability for your business. |
|
Cybersecurity Solutions |
Advanced security strategies and solutions to protect your enterprise from cyber threats and data breaches. |
|
Network Design and Implementation |
Expert design and deployment of robust network infrastructures to support your business operations. |
|
Data Management and Analytics |
Innovative data management and analytics services to help you make informed business decisions. |
|
Custom Software Development |
Tailored software development services to meet your business requirements and objectives. |
|
Technology Consulting |
Strategic technology consulting to align your IT investments with your business goals. |
|
Digital Transformation |
Services to guide your business through digital transformation, enhancing digital capabilities and competitiveness. |
For all businesses:
Whether you are in the legal, real estate, construction, automation, retail, or entrepreneurial field, our solutions adapt to you!

Telephone integration and management in Microsoft Teams
Your existing numbers can be ported to the Microsoft platform. Receive and make calls directly in MS Teams.

Configuring and managing roles and access in SharePoint
Access management, role creation and migration of your data from a local server or another cloud platform, such as Google Drive or Dropbox.
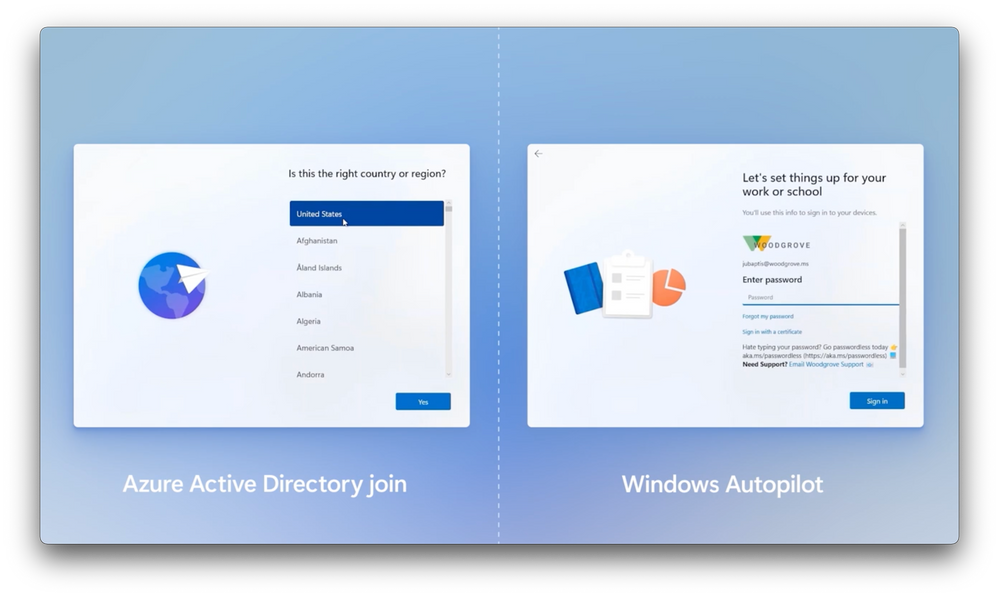
Automatic management and configuration of your workstations with Microsoft Autopilot
Autopilot is a collection of technologies used to configure and pre-configure new devices, preparing them for productive use as soon as a user logs on with their corporate information.
It simplifies the deployment process for Windows devices, eliminating the need for image creation and manual installation processes.
Autopilot enables organizations to personalize the setup experience and reduce the time it takes to get devices ready for use.
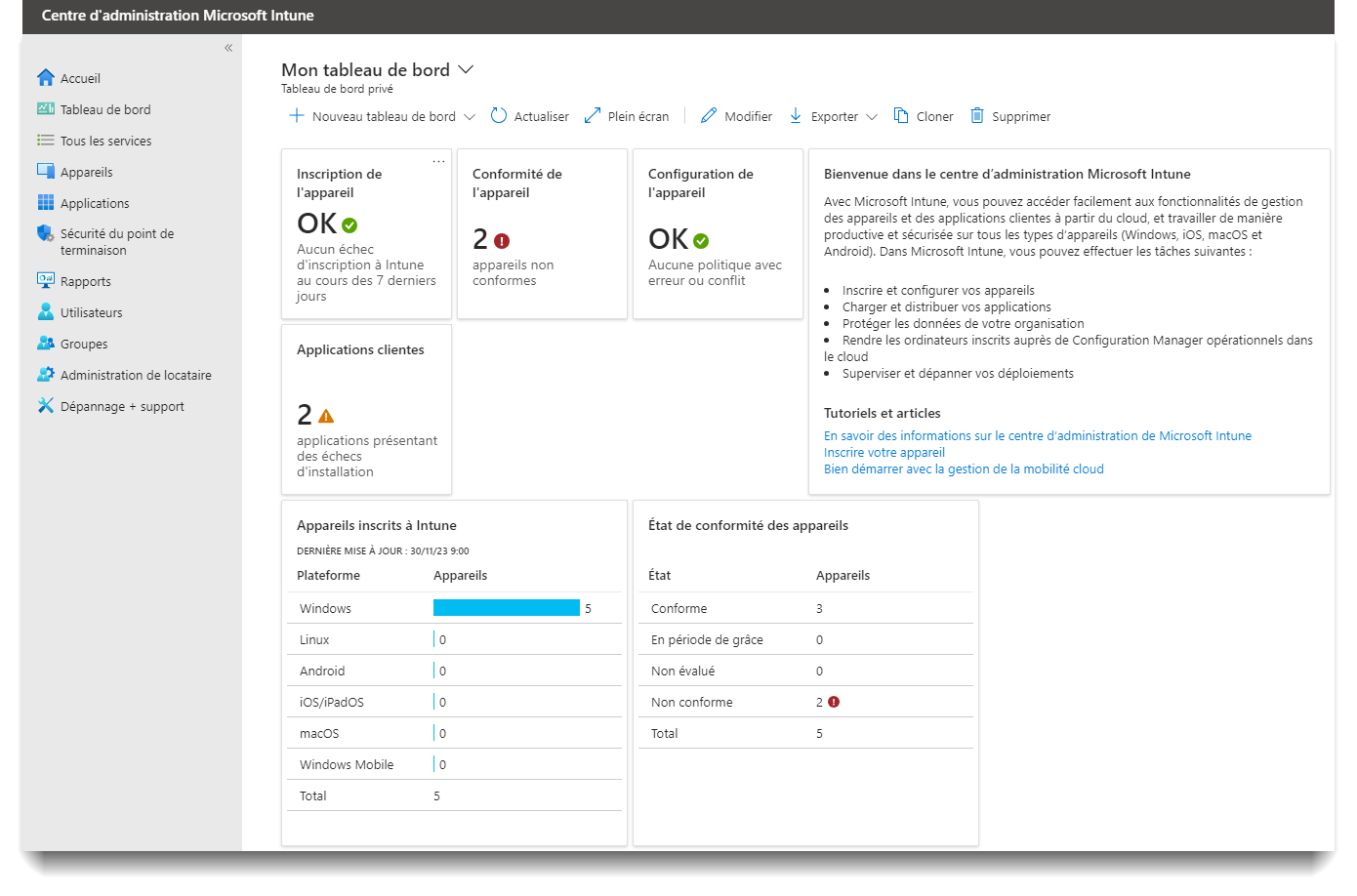
Configuring Microsoft Intune to deploy your software on your devices
Intune is an Enterprise Mobility Management (EMM) service, part of Microsoft's Enterprise Mobility + Security (EMS) solution. It enables organizations to manage their employees' devices (mobile, desktop) and applications.
It offers mobile application management (MAM) and mobile device management (MDM). This includes the deployment, configuration, monitoring and updating of applications and devices.
Intune also supports identity and access management, enabling secure authentication and protection of corporate data.

Managing and migrating your e-mails from the most popular platforms
Whether your e-mails are hosted in WordPress, Google Gmail, Videotron, Bellnet or Yahoo Mail, we can migrate your e-mails without service interruption.

Your Microsoft tenant is hosted at GoDaddy and you don't have access to the full portfolio?
We can help: Ask for CSP opt-in and regain control of your tenant!

Efficient management of your local workstations and servers using Datto RMM.
This option is available on a monthly per device subscription basis.
Datto RMM (Remote Monitoring and Management) is a platform designed for Managed Service Providers (MSPs) and IT professionals to remotely monitor, manage, and maintain their clients' computer systems. Here are some advantages of Datto RMM for managed users:
-
Proactive Monitoring: Datto RMM allows MSPs to real-time monitor the status of their clients' computer systems. This means they can detect potential issues before they become major problems, minimizing downtime and interruptions.
-
Task Automation: The platform offers powerful automation features, enabling MSPs to automate recurring tasks such as software updates, backups, patch management, and more. This reduces manual workload and saves time.
-
Remote Management: MSPs can remotely access their clients' systems to perform maintenance tasks, troubleshooting, and updates without the need to be physically on-site. This allows for quick issue resolution and efficient support.
-
Enhanced Security: Datto RMM provides advanced security features, including threat detection and security patch management. This helps maintain systems securely and protect sensitive data.
-
Reporting and Compliance: The platform generates detailed reports on system status, allowing MSPs to track performance, meet compliance requirements, and demonstrate the value of their services to clients.
-
Scalability: Datto RMM is designed to scale with your business needs. It can handle a large number of client systems, making it suitable for MSPs of all sizes.
Get instant visibility of employee productivity and engagement with Activtrak
This option is available on a monthly per device subscription basis.
Advantages of ActivTrak Software:
-
Activity Monitoring: ActivTrak allows you to monitor employee activity on their computers, including visited websites, used applications, and time spent on each task. This can help businesses gain a better understanding of how their employees spend their work time.
-
Increased Productivity: By identifying inefficiencies and distractions, ActivTrak can contribute to improving employee productivity. Managers can provide data-driven feedback to help employees manage their time more effectively.
-
Data Loss Prevention: ActivTrak can be used to monitor potentially risky activities, such as downloading sensitive files or copying confidential data. This can help prevent data loss and information leaks.
-
Regulatory Compliance: In some industries, it may be necessary to track and document employee computer activity to comply with privacy and security regulations. ActivTrak can assist businesses in meeting these requirements.
-
Security Issue Identification: By monitoring suspicious or unauthorized activities, ActivTrak can help detect potential computer security threats, such as intrusion attempts or malicious behavior.
-
Trend Analysis: ActivTrak offers analysis tools that allow businesses to track long-term trends in computer usage. This can help make informed decisions to improve operations.
-
Flexibility: ActivTrak software provides flexibility in how it can be configured to monitor employees. Companies can customize rules and alerts to meet their specific needs.
-
Transparency: Using ActivTrak can promote transparency within the company as employees are informed about the monitoring and may become more aware of their computer usage at work.
Need help with your Bill 25 compliance process?
We can help you with the drafting of your directives and the governance of your IT systems.
We have templates for this! Call us and we'll send them to you free of charge! (in french)
- L'aide-mémoire pour la loi 25 (Obligations Québec) - Memo for Law 25 (Quebec Obligations)
- L'aide-mémoire pour la loi 25 (Obligations Canada) - Memo for Law 25 (Canadian Obligations)
- Les notions de sécurité informatique de base - Basic Computer Security Concepts
- Template: Directive relative à la protection des données sensibles et à la confidentialité (à mettre à vos couleurs) - Template: Directive on the Protection of Sensitive Data and Confidentiality (to be customized with your colors)
- Template: Directive d'utilisation des ressources informatiques (à mettre à vos couleurs) - Template: IT Resource Usage Directive (to be customized with your colors)
- Loi 25- Guide de départ - Law 25 Starter Guide
- Plan de recouvrement - Recovery Plan

Zero trust VPN
Need secure access to your office or a shared workspace such as:
Regus, Le Local, Le Cornélien, Halte 24-7, Temps libre Mile End, Café Insiders, Crew Collective & Café, Café Collab, Anticafé Montréal, Espace Koala, Cowork Québec, Bnkr Coworking, École d'entrepreneuriat de Québec, AV3 Coworking, Espace Niviti or almost any Coworking space?
"It's time to ditch your VPN."
Welcome to Twingate, the vpn that requires no opening of network ports on your NAT network, even with double NAT router layers!
Several customers have asked us for an access solution for shared offices. We have the solution!
The term "Zero Trust" generally translates as "Confiance Zéro" or "Zero Confidence". It's an approach to IT security that challenges the traditional principle of implicit trust in users and devices within a network, adopting instead an approach of distrust towards everything, even within the network, and requiring constant verification of identity and authorization to access resources. We support major GIAs such as Google, Microsoft, Linkedin to authenticate into the platform.
The platform integrates seamlessly with Okta, Microsoft and G-Suite for SSO authentication.
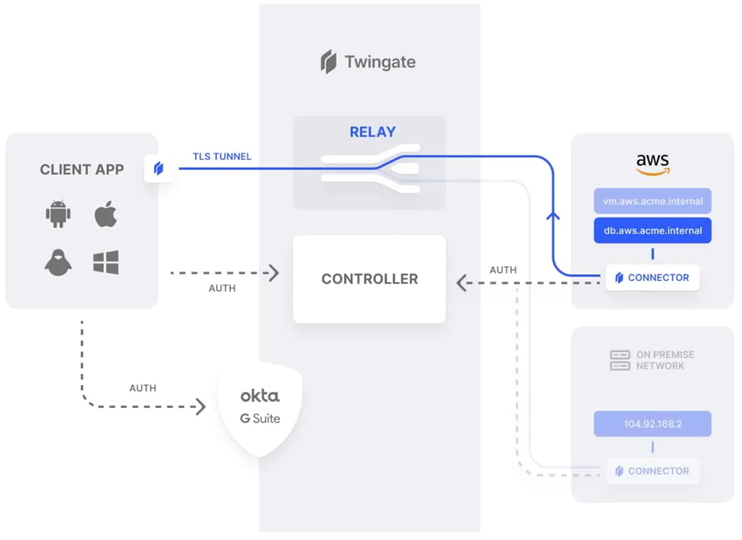
To understand how this works, we'll provide two examples:
- In our first example, an end-user running Twingate on his laptop from home makes a request for corporate resources.
- The Twingate client detects that the request is for a company resource and sends the request to the Controller. The Controller checks the user's authorizations and the Connector's access policy. If all is in order, the Controller grants the request and forwards it to the Connector. The Connector then validates the client's connection, resolves the DNS request and grants access to the requested resource via the Relay, over a TLS tunnel.
- In our second example, an end-user running Twingate loads a YouTube video into his browser.
- In this case, the Twingate client detects that the request is not for a defined corporate resource and simply sends the traffic via the default route - over the regular Internet.
On-site technical support
If your computer no longer works, we will travel within a radius of 50 km
* Minimum 1 hour
Would you rather visit us?
Technicians with 20 years experience, located in Quebec.
Any type of computer problem, starting at $88.95 per hour. Subject to conditions.
Support@distance and appelezletech have been in business since 20 years.
Most repairs within 48 hours.
What are the 3 levels of IT support we offer?
The three commonly used levels of IT support are:
Level 1: Also known as "first-line support," this level of support is usually the first point of contact for end-users. Level 1 staff is responsible for opening support tickets, identifying and resolving simple issues, and escalating more complex issues to Level 2.
Level 2: Also known as "second-line support," this level of support consists of more experienced technicians and engineers who can handle more complex issues than those at Level 1. Level 2 staff is typically responsible for escalating more difficult problems and working closely with Level 3 to resolve the most critical issues.
Level 3 : Also known as "third-line support," this level of support consists of highly skilled experts and engineers who are capable of resolving the most critical and complex issues. Level 3 staff is typically responsible for escalating the most difficult problems and managing large-scale technical projects.